
A whistleblowing alert is a stress test of your compliance program. Not because every report is true, but because regulators, auditors, courts, and employees will judge you on how you respond: how fast you triage, how fairly you investigate, how consistently you enforce, and how well you prevent the issue from happening again.
For mid-sized and even big companies, internal investigations can quickly become chaotic (emails in one place, HR files in another, decisions made in meetings with no audit trail). The result is often the worst of both worlds: high disruption and low defensibility.
This guide explains what good looks like in 2026: a disciplined investigation process after a speak-up report, a principled approach to consequences, and a root-cause analysis that feeds back into your risk assessment and internal controls across frameworks like Loi Sapin II, ISO 37001, UNE 19601/UNE 19603.
Why internal investigations matter after a whistleblowing alert
A whistleblowing channel is not just a mailbox. Under laws and guidance based on the EU Whistleblowing Directive (Directive (EU) 2019/1937), organisations are expected to have a reliable process to receive, follow up, and close reports, while protecting confidentiality and preventing retaliation.
Beyond whistleblowing rules, investigation capability is also a credibility signal under major compliance frameworks:
- Loi Sapin II expects an effective anti-corruption program, and in practice that includes the ability to detect and respond to misconduct, not only publish policies.
- ISO 37001 (anti-bribery) requires processes for reporting, investigating, and dealing with bribery-related concerns.
- UNE 19601 (criminal compliance) and UNE 19603 (antitrust compliance) emphasise response, discipline, remediation, and continuous improvement.
Most importantly, internal investigations protect the business. They help you:
- Stop harmful conduct early (corruption, cartel contacts, money laundering red flags, AI misuse)
- Avoid repeating failures by fixing the real cause, not just the symptom
- Preserve trust in speak-up channels (and reduce the risk of external escalation)
Before you start: triage the alert like a case, not a rumor
The first hours matter. The goal is not to prove or disprove the allegation immediately, but to make sure you respond proportionately and preserve options.
Confirm intake quality and confidentiality
Check whether the report includes enough detail to act. If the report is anonymous and your channel allows two-way messaging, use it to request clarifications (dates, teams, systems, names, third parties, relevant documents).
Confidentiality is a core expectation. Limit access to those who genuinely need to know, and be disciplined about where information is stored.
Decide whether it is an investigation, a HR issue, or a control failure
Not every alert is misconduct. Some are misunderstandings, performance complaints, or process issues. You still need follow-up, but the path differs.
A helpful filter is:
- Potential legal or regulatory exposure (bribery, bid rigging, AML red flags, harassment, sanctions, data misuse)
- Senior management involvement (higher independence requirements)
- Risk of evidence loss (need for immediate preservation)
- Risk of retaliation (protect the reporter and witnesses)
Put evidence preservation first
If there is a risk that emails, chat logs, approvals, expense records, CRM notes, or procurement files could be deleted or altered, implement a legal hold or preservation steps consistent with your IT and legal policies.
In practice, many investigation failures come from starting interviews before preserving the digital trail.
How to run an internal investigation that holds up
A strong investigation is not defined by volume (more interviews, more documents). It is defined by fairness, traceability, and a defensible reasoning chain from allegation to conclusion.
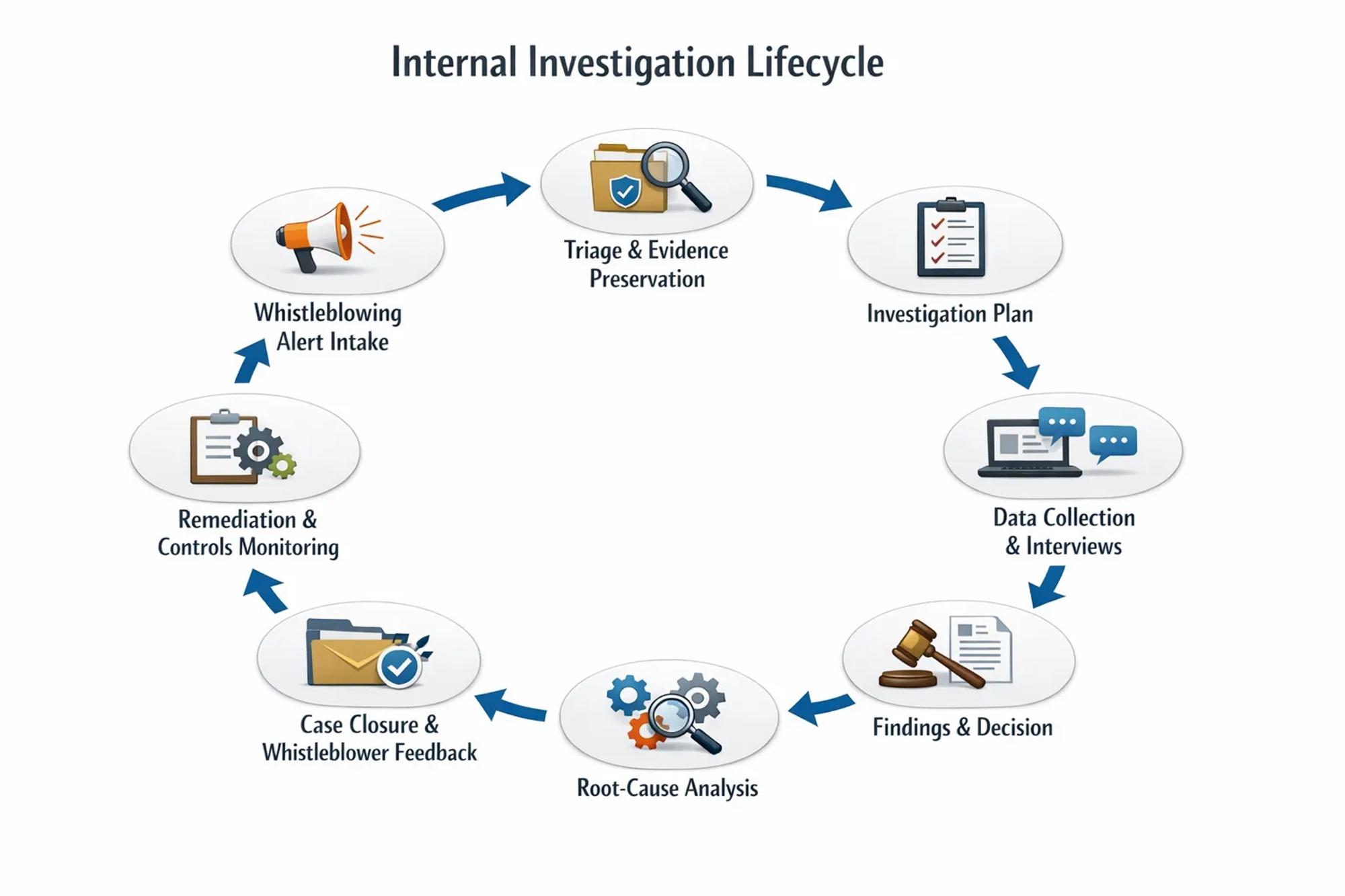
Step 1: Set governance and independence
Decide who leads the investigation and who supervises it.
Independence is not a buzzword. If the alleged misconduct touches senior leaders, revenue owners, or sensitive commercial topics (like antitrust), consider:
- Assigning an investigator outside the reporting line of implicated persons
- Involving legal counsel early to manage privilege where applicable
- Using external investigators for high-risk matters (or when internal neutrality is questioned)
Also align on who will approve outcomes (HR, compliance, legal, management, board committee). Ambiguity here creates delays and inconsistent decisions.
Step 2: Define scope and an investigation plan
Write down the basics before you collect information:
- Allegation summary and risk area (anti-corruption, antitrust, AML, AI governance)
- Time period and entities (subsidiaries, countries, third parties)
- Key questions to answer (what happened, who knew, what policy was breached)
- Data sources to review (systems, shared drives, finance tools, messaging platforms)
- Interview list and sequencing
A plan keeps the process proportionate, and it helps you explain later why your investigation was reasonable.
Step 3: Collect data in a way you can explain
Data collection is where defensibility is won or lost. Even if you are not doing forensic imaging, you should still be able to show:
- What you collected
- From where
- Who had access
- How you avoided cherry-picking
For example, in an anti-corruption allegation, expense claims alone are rarely enough. You often need approvals, vendor onboarding records, contract scope, and business justification. In antitrust allegations, meeting calendars, trade association participation, chats, and shared documents are frequently more probative than formal emails.
Step 4: Run interviews that are fair and useful
Interviews should test hypotheses, not confirm them.
Good practice includes:
- Explaining the purpose of the interview and confidentiality expectations
- Avoiding promises you cannot keep (for example, absolute confidentiality)
- Using consistent interview notes and secure storage
- Offering the interviewee the opportunity to share documents or context
Coordinate closely with HR and legal on employee rights, local labor rules, and any works council implications.
Step 5: Make findings based on a clear standard
Decide upfront what “substantiated” means for your organisation. Many teams use practical standards such as “more likely than not” for internal policy breaches, while keeping an eye on legal thresholds when relevant.
Your findings should clearly separate:
- Facts (what evidence shows)
- Inferences (what you conclude from the facts)
- Policy or control breaches (what internal rule was violated)
- Open items (what could not be confirmed)
This separation is essential when lawyers, auditors, or regulators review your work.
Step 6: Document the case like you may need it in two years
Investigations often become important long after closure (audits, litigation, certification, debarment disputes, M&A due diligence).
A solid case file typically includes:
- Intake record and triage rationale
- Preservation actions
- Investigation plan and scope changes (with reasons)
- Evidence list and interview log
- Findings memo or report
- Decisions and approvals
- Remediation actions and follow-up testing
If your organisation struggles with manual tracking, it is usually a sign you need workflow discipline and automated evidence collection (not “more spreadsheets”).
How to decide consequences for violations of internal policies
Consequences are where compliance, HR, and legal must align. If outcomes appear arbitrary, you create three risks at once: employee distrust, whistleblowing channel collapse, and regulator skepticism.
Start from principles: proportionality and consistency
Two things can be true at the same time:
- You must treat people fairly (context matters)
- You must treat similar cases similarly (consistency matters)
To achieve that, define decision factors and apply them consistently.
Decision factor | What to assess | Why it matters |
|---|---|---|
Severity and harm | Financial impact, customer harm, market impact, competition distortion, public procurement exposure | Drives proportionality and escalation |
Intent | Error, negligence, reckless disregard, deliberate misconduct | Separates training gaps from integrity failures |
Seniority and role | “Tone at the top” responsibilities, control ownership, fiduciary duties | Leaders are held to higher expectations |
Pattern vs isolated | First occurrence, repeated behavior, prior warnings | Indicates cultural or individual risk |
Cooperation | Honesty, document preservation, willingness to remediate | Affects trust and future risk |
Control circumvention | Bypassing approvals, falsifying records, using shadow channels | Signals design or oversight weaknesses |
Third-party involvement | Agents, distributors, trade associations, vendors | May require contractual action and due diligence remediation |
Match outcomes to the type of breach
A practical outcome set often includes:
- Employee actions: coaching, targeted training, formal warning, role change, bonus impact, termination
- Managerial actions: accountability for supervision failures, control ownership consequences
- Third-party actions: remediation plan, enhanced monitoring, contract suspension or termination
- Program actions: policy clarification, control redesign, monitoring increase
Where relevant, you also need a decision on external reporting (for example, regulatory notification duties, suspicious activity reporting in AML contexts, or cooperation considerations).
Avoid two common mistakes
First, do not treat discipline as the only “consequence.” Regulators often look for program improvement, not only punishment.
Second, do not let outcomes be negotiated informally between functions. If HR, legal, and compliance do not share a structured decision model, you will get inconsistent results across countries and business units.
Root-cause analysis: the step most teams skip (and regulators notice)
Closing a case without root-cause analysis is like fixing a leak by repainting the ceiling.
Root-cause analysis answers the question: why did this happen in our system? Not only “who did it?”
This is where internal investigations connect directly to risk assessment and internal controls.
What “root cause” looks like in compliance
In compliance cases, root causes typically fall into a few categories:
- Risk assessment gap: the risk existed but was not identified, or it was scored too low
- Policy gap: policy missing, unclear, outdated, or not tailored to real workflows
- Control design gap: control exists but is easy to bypass, or lacks segregation of duties
- Control execution gap: control exists but is not performed, documented, or supervised
- Monitoring gap: KPIs exist but do not detect failures early, or are not reviewed
- Culture and incentives: targets or leadership signals encourage rule-bending
- Training gap: people did not understand the rule or the red flags (this is where well-designed risk management training matters)
Use a simple method that drives action
You do not need complex Six Sigma tooling to do this well. What matters is discipline.
Two approaches that work well for mid-sized compliance teams:
- Five whys: repeatedly ask “why” until you reach a process, governance, or incentive failure you can fix.
- Cause categories: classify the root cause (policy, control design, control execution, monitoring, culture), then assign remediation per category.
The key is that your root-cause statement should be actionable. “Lack of awareness” is not a root cause unless you specify which role, which scenario, and which training or workflow failed.
Turning root cause into remediation: update risk assessment and controls
A completed investigation should feed directly into your compliance operating model.
Update your risk assessment with what the case revealed
If your organisation maintains a compliance risk map, the investigation may require you to:
- Add a new scenario (for example, “trade association benchmarking used to exchange sensitive information”)
- Increase likelihood due to demonstrated occurrence
- Adjust impact due to business consequences
- Re-score residual risk if controls proved ineffective
If you need a structured approach to refresh your risk map, Naltilia has a practical guide on how to build a compliance risk map in 6 steps.
Put remediation into a tracked action plan
Remediation should be managed like a project with owners, deadlines, evidence, and effectiveness testing. Otherwise, it becomes “paper remediation,” which looks good until the next audit.
A useful structure is corrective and preventive actions:
- Corrective actions fix the specific failure (for example, terminate a risky third party, recover funds, correct a report).
- Preventive actions reduce recurrence (for example, redesign approvals, increase monitoring, add targeted training, strengthen third-party controls).
Examples of remediation by framework (what “good” can look like)
Risk area and framework | Typical investigation trigger | Root-cause remediation examples |
|---|---|---|
Anti-corruption (Loi Sapin II, ISO 37001) | Gifts, hospitality, agents, suspicious invoices | Tighten approval thresholds, improve third-party due diligence workflow, add audit trails for sponsorships, monitor high-risk payments |
Criminal compliance (UNE 19601) | Fraud, embezzlement, misconduct with criminal exposure | Clarify delegations of authority, strengthen segregation of duties, improve case management evidence, increase controls testing |
Antitrust (UNE 19603) | Trade association behavior, dawn raid signals, RPM, sensitive exchanges | Pre-clear agendas, implement meeting minutes discipline, train commercial teams on “no-go” topics, monitor communications in high-risk contexts |
AML | Internal escalation of KYC gaps or transaction anomalies | KYC refresh cadence, improve documentation standards, tune monitoring rules, strengthen escalation and approvals |
AI governance (EU AI Act) | AI system used without oversight, poor documentation, model drift incidents | Maintain AI inventory, define human oversight controls, improve logging and incident response, assign accountable owners |
Test control effectiveness after remediation
Remediation is not complete when the action is marked “done.” It is complete when you can show it works.
That means defining what evidence you will collect going forward (approvals, logs, attestations, monitoring results) and how often you will review it. If you are building a more measurable program, you may find it useful to align remediation tracking with board-level metrics, like those described in compliance dashboard risk metrics your board actually cares about.
Where technology helps (without replacing judgment)
Internal investigations require judgment, especially for credibility assessments, interview strategy, and outcome decisions. But technology can remove friction and make your process defensible.
In practice, teams benefit most from tools that:
- Centralize case records and evidence
- Automate data collection for controls connected to the case
- Track remediation actions with owners and deadlines
- Connect findings back to risk assessments and policies
Naltilia’s platform is designed for this operational side of compliance, including regulatory risk assessment, remediation actions, tailor-made policies, automated data collection, and compliance workflow automation.
Frequently asked questions
How fast should we acknowledge a whistleblowing report? Many whistleblowing regimes require timely acknowledgment and follow-up. According to the EU Whistleblowing Directive (Directive (EU) 2019/1937), complaint should be acknowledge not later than 7 days since receipt. Even when a strict deadline does not apply to you, early acknowledgment (and a clear next-step message) is a best practice to maintain trust and reduce escalation risk.
When should we use external counsel for an internal investigation? Consider external support when senior leaders may be implicated, when independence is questioned, when the matter is cross-border or high-stakes, or when you need specialised skills (forensics, antitrust, AML) and privileged legal advice.
How do we protect confidentiality while still interviewing witnesses? Limit access to case information, share only what is necessary for each interview, keep records in a restricted repository, and remind participants about confidentiality expectations. You can also make them sign and NDA. Avoid informal discussions outside the investigation team.
What is the difference between a policy breach and a control failure? A policy breach is non-compliance with an internal rule (code of conduct, gifts policy, competition policy). A control failure means a preventive or detective mechanism did not work (approval was bypassed, monitoring did not flag, evidence was missing). One case can involve both.
Do we have to discipline every breach the same way? You should be consistent, not mechanical. Similar cases should lead to similar outcomes, while still considering intent, harm, seniority, recurrence, and cooperation.
How does root-cause analysis help in audits or certifications (ISO 37001, UNE 19601/19603)? It shows continuous improvement. Auditors and regulators often look for proof that incidents lead to changes in risk assessment, controls, and monitoring, not only to a closed case file.
How do we ensure remediation actions actually happen after the investigation? Assign a single owner, set deadlines, require evidence for closure, and run effectiveness tests. Workflow automation and automated evidence collection reduce the risk that actions remain “agreed” but unimplemented.

